Most WordPress security guides start with the same advice: keep your plugins updated, use strong passwords, and install an SSL certificate. That advice is fine. It's also completely insufficient for advocacy organizations.
Advocacy website security requires a different approach because the threat is different. Your site isn't just being scanned by random bots looking for vulnerable WordPress installations. It's being targeted by people who want to silence your message, disrupt your fundraising, or expose your supporters. That distinction changes everything about how you need to think about protection.
We've managed websites for national advocacy organizations, political action committees, and issue campaigns for nearly two decades. That experience includes targeted DDoS attacks, attempted shutdowns of donation pages, and one incident serious enough to involve the FBI. The gap between standard nonprofit security practices and what advocacy organizations actually need is dangerously wide.
"You're essentially planning to be reactionary, which is a funny thing to say, but that's exactly what it feels like working with these clients."
That framing captures the reality. You can't predict when your issue will become the lead story on cable news or when a political figure will mention your organization by name. But you can build the security infrastructure that holds when it happens.
Why Advocacy Organizations Face a Different Threat

A local food bank and a national reproductive rights organization might both run WordPress. They might even use the same hosting plan and the same security plugins. But their threat profiles aren't in the same category.
Nonprofits rank as the second-most targeted sector according to Okta's 2025 report, and Microsoft's Digital Defense Report places them fourth among sectors targeted by nation-state actors. Those rankings place advocacy organizations alongside government agencies and critical infrastructure, not small businesses with basic web presences.
The numbers are accelerating:
- Nonprofits experienced a 30% year-over-year increase in weekly cyberattacks in 2024
- Cloudflare's Project Galileo reports a 241% increase in cyberattacks between 2024 and 2025, with human rights and civil society organizations the second most impacted category
- Between May 2024 and March 2025, Cloudflare blocked 108.9 billion cyber threats against organizations in the program, averaging 325.2 million attacks per day
- In a single three-day period in early 2026, hacktivist groups launched 149 DDoS attacks against 110 organizations across 16 countries
What makes this uniquely challenging isn't just the volume. It's the motivation behind it.
Adversaries Who Are Funded and Motivated
Standard website attackers are opportunistic. They scan for vulnerabilities, exploit what they find, and move on. Adversaries targeting advocacy organizations have specific political or ideological reasons to attack, and many have the resources to sustain campaigns over days or weeks.
The threat is state-level:
- Star Blizzard (Russian-linked) targeted over 30 civil society organizations between 2023 and 2024 using spear-phishing campaigns
- Mustang Panda (Chinese) targeted government officials and NGOs in Southeast Asia
- APT42 (Iranian state-sponsored) launched phishing campaigns impersonating journalists and event organizers to target NGOs and activists
These aren't script kiddies. These are state-backed operations.
Your Success Makes You a Target
Here's the part that generic security guides never address: the more effective your advocacy work, the more likely you are to be attacked. Your public stance on issues creates a targeting signal. When your campaign gains traction, when your message reaches the public, when your fundraising succeeds, you become more visible to adversaries who want to stop you.
Attacks are deliberately timed to coincide with your highest-stakes moments: legislative pushes, fundraising campaigns, media coverage, and mobilization events. The attackers understand when your site matters most, and that's exactly when they strike.
The threshold for attracting this kind of attention is lower than most organizations assume.
"Controversial doesn't have to be particularly radical to attract someone who wants to take you down."
"You never know when your topic is going to get hot. You never know when a member of the media will pick up your story, when a candidate will say something positive or negative, or what kind of attention you're going to receive."
The Preparedness Gap
Despite facing serious threats, advocacy organizations typically operate with security postures designed for a much lower threat level:
- 70% of nonprofits don't have basic cybersecurity policies in place
- MFA adoption among small organizations sits at approximately 27%, compared to 87% at organizations with 10,000+ employees
- The average nonprofit data breach goes undetected for 467 days
The CyberPeace Institute and CrowdStrike have described nonprofits as "cyber-poor, target-rich." That captures the problem precisely. Security postures remain at small-business levels, while the threats are enterprise-grade.
How Advocacy Websites Get Attacked
Understanding specific attack types matters because each one demands a different defense. Generic "website security" advice lumps them together, but the responses couldn't be more different.
Targeted DDoS: Silencing Through Overwhelming Traffic

Distributed Denial of Service attacks against advocacy sites aren't about extortion. They're about silencing. The goal is to take the site offline precisely when the organization needs to communicate, mobilize, or fundraise.
We've seen this firsthand. DDoS is the most common targeted attack against our political and advocacy clients. The attackers aim to stop the organization from sharing its message, distributing its content, or, most critically, collecting donations.
"We had the FBI involved because the attack against the donation page was determined to be a direct threat to the democratic process. This is not something to be taken lightly."
The donation window makes this concrete. After a television spot or a national news appearance, donations may surge for just five to ten minutes. That's the entire window. A DDoS attack that takes the donation page offline during that surge can cost the organization its most critical fundraising moment.
DDoS attacks targeting advocacy organizations look different from typical volumetric attacks. They are timed to high-stakes moments, politically motivated rather than financially motivated, potentially sustained for days or weeks, and increasingly sophisticated in their techniques.
This has played out repeatedly:
- 2014: Hong Kong's PopVote polling platform was hit with a massive 500 Gbps DDoS attack before the Umbrella Movement protests, and Telegram (used by protest organizers) was hit within an hour of a police-protester clash, deliberately timed to disrupt coordination when communication was most critical
- 2018: Hackers launched DDoS attacks against Democratic political campaigns timed to coincide with online fundraising periods
- 2024: A pro-Russian hacker group attacked Dutch political websites on election day
- 2025: A human rights organization was targeted by a 12-day sustained attack delivering over 2.7 billion requests
These aren't hypothetical scenarios.
Defacement: Putting the Attacker's Message Where Yours Should Be
An advocacy organization's website is its message. Defacement doesn't just disrupt operations; it replaces that message with the attacker's. For organizations whose credibility depends on public communications, the reputational damage goes well beyond the technical disruption.
Defacement is routinely used as a political weapon:
- 2013: The Syrian Electronic Army, a hacktivist group supporting Syrian president Bashar al-Assad, defaced multiple U.S. media and organizational websites, treating defacement as a tool for advancing political interests.
- 2024: The hacktivist group Stucx Team defaced the homepages of several French websites just three days after the arrest of Telegram CEO Pavel Durov, showing how fast these campaigns spin up in response to political events.
The more dangerous variant is subtle content manipulation. Rather than crude political graffiti, sophisticated attackers can make small changes to an organization's published content: altering policy positions, changing statistics, or modifying calls to action. These subtle defacements may go undetected for longer and cause more damage than an obvious hack.
In our own experience, we haven't had a defacement succeed. The attempts are there, and we find injection clues in our logs, but because we've always used Cloudflare Enterprise, Imunify360, and quality hosting infrastructure, we've been able to prevent them. That's the point: prevention is the story, not recovery.
Donor Data Exfiltration: The Highest-Stakes Target
Advocacy organizations hold uniquely sensitive data. Beyond names, addresses, and emails, a donor database reveals political affiliations and beliefs. Donating to an advocacy organization is a political statement, and exposing that data can put donors at real risk, particularly for organizations working on controversial issues.
Recent breaches show the scale of the risk:
- The DonorView breach exposed 948,029 records, including donation information and payment details
- The Blackbaud ransomware attack exposed personal data from approximately 6 million clients across numerous nonprofit organizations
- The average nonprofit data breach costs $2 million
For advocacy organizations, the obligation to protect donor data goes beyond legal requirements. A donor who gives to a controversial cause and has their information exposed faces potential personal consequences: harassment, employment discrimination, or worse. Donor data protection isn't a compliance exercise. It's a mission-critical responsibility.
PCI DSS 4.0 compliance has been mandatory since March 2025 for any organization accepting credit card donations. Nonprofits using third-party payment processors have a reduced compliance burden but are still responsible for ensuring that their website and vendors meet standards. Non-compliance penalties range from $5,000 to $500,000.
Credential Attacks: Getting In Through Staff Accounts
Advocacy staff are social engineering targets in ways that typical employees of small organizations aren't. Their email addresses are published for outreach. Their org charts and bios are public. They regularly communicate with journalists, donors, and officials, which makes spear-phishing impersonating these contacts harder to distinguish from legitimate outreach.
81% of users reuse passwords across multiple sites. When advocacy staff reuse passwords, a breach at another service can create credentials that work on the organization's WordPress site. A successful credential stuffing attack on a WordPress admin account gives the attacker full control: content modification, user data access, malware installation, and the ability to lock out legitimate administrators.
The specific pretexts used against advocacy organizations are designed to exploit the nature of the work:
- Impersonating journalists requesting interviews or comments on the organization's issues
- Posing as potential major donors requesting information about programs
- Faking urgent requests from board members or executive directors
- Mimicking partner organization communications about joint campaigns
- Impersonating government officials regarding regulatory compliance
Each of these scenarios mirrors legitimate communications that advocacy staff receive every day, which is exactly what makes them effective.
AI-enhanced attacks are making this worse. Attackers now use AI to craft convincing phishing emails and spoofed voice messages tailored to specific organizations. Telling AI-crafted spear-phishing apart from legitimate outreach is getting harder every month.
Why Standard Nonprofit Security Advice Falls Short
Every nonprofit website security guide covers the same ground: install an SSL certificate, keep WordPress updated, use strong passwords, and run a security plugin. This advice is necessary. It's also the equivalent of locking your front door when you're facing adversaries with the tools and motivation to come through the walls.
The gap in existing security guidance is striking:
- Advocacy-focused digital safety resources cover personal security, encrypted messaging, VPNs, and safe browsing, but ignore website infrastructure entirely
- Nonprofit website security guides cover CMS hardening and plugin updates, but treat all nonprofits identically, making no distinction between a community garden and a political action committee facing state-level adversaries
No one's connected these two worlds. The intersection of advocacy-specific threat awareness and practical website infrastructure security is where the real guidance is needed.
What Table-Stakes Security Covers
Standard WordPress security practices protect against opportunistic, automated attacks:
- Keeping WordPress core, plugins, and themes updated closes known vulnerabilities
- Strong, unique passwords prevent basic brute-force attacks
- SSL encryption protects data in transit
- Regular backups enable recovery from incidents
- Security plugins like Wordfence provide basic monitoring and firewall rules
These measures stop the automated scanners. They don't stop a funded adversary who's specifically targeting your organization during a critical campaign moment.
What Advocacy Organizations Actually Need
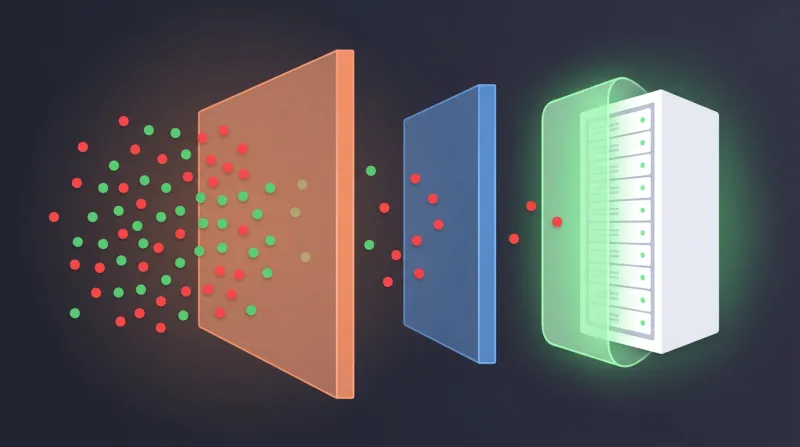
Protection against targeted attacks requires layers that standard guides never discuss:
Edge-level filtering. A web application firewall that inspects every request before it reaches your server. In 2024, 7,966 new WordPress plugin vulnerabilities were registered, a 34% increase over 2023. The weighted median time from disclosure to first exploit is just 5 hours, and plugin developers failed to provide timely fixes for 46% of them.
A WAF buys you time by blocking exploitation attempts even when the underlying vulnerability exists.
DDoS mitigation. The ability to absorb volumetric attacks and rate-limit application-layer attacks without affecting legitimate traffic. Non-negotiable for any organization that has faced or expects to face targeted attacks.
Bot management. Distinguishing between legitimate traffic (donors, supporters, search engines) and malicious bots (credential stuffing, scraping, vulnerability scanning). During a media-driven traffic spike, you need systems that can tell the difference between 10,000 supporters responding to a call to action and 10,000 bots trying to take down your donation page.
Real-time monitoring with rapid response. Automated tools catch known patterns. Human monitoring catches novel attacks that no automated system anticipated. For advocacy organizations, the ability to respond to an active attack in real time, not after hours or the next business day, is the difference between a minor incident and a catastrophic one.
The Advocacy Website Security Stack That Actually Works
Our security approach for advocacy clients operates on multiple layers. A single layer of protection isn't an option when your clients receive direct, targeted attacks.
Cloudflare Enterprise WAF at the edge. Every request is inspected before it reaches the server, blocking SQL injection, cross-site scripting, remote code execution, and other web application attacks. For advocacy organizations, the key advantage is the ability to configure rules that distinguish between legitimate traffic surges, such as a successful email blast driving donors to the site, and attack traffic. This isn't something you set once and forget. It requires ongoing tuning based on the organization's actual traffic patterns and the threats active at any given time.
Cloudflare CDN for static assets. Offloading images, CSS, and JavaScript from the server means that during a traffic spike or attack, the server only handles what it absolutely must: usually the donation processing that matters most.
Imunify360 on the server. This handles real-time malware scanning and automatic cleanup. If something gets past the edge layer, Imunify360 catches it at the server level.
Server-level firewall. An additional barrier providing defense in depth.
24/7 monitoring with rapid response capability. This is where managed security differs from self-managed tools. We monitor for anomalies and respond to active attacks: adjusting WAF rules in real time, scaling resources, and coordinating with the organization's communications team.
"This is not a nine-to-five support job. It's not 'we'll scale later.' Everything has to be in place. Monitoring has to be in place. Response protocols have to be in place. None of it can wait."
"The infrastructure has to be there. It cannot be an afterthought, and it cannot be something you plan for reactively. It has to simply be in place."
Free and Low-Cost Protection Options
Not every advocacy organization needs or can afford enterprise-grade security from day one. But there are meaningful free resources:
Cloudflare Project Galileo provides free Business-level protection, including WAF and DDoS mitigation, to qualifying organizations working in human rights, civil society, journalism, or democracy. Currently protecting over 2,900 internet properties, it's an excellent option for qualifying organizations. Partner organizations like the EFF, CDT, and Access Now vet applicants.
Cloudflare for Campaigns, through a partnership with Defending Digital Campaigns, offers free protection to qualifying political campaigns.
CISA resources from the federal Cybersecurity and Infrastructure Security Agency provide tools and guidance specifically for high-risk communities, including civil society organizations.
These programs validate a key point: federal agencies and major technology companies recognize that advocacy organizations face real cyber threats. The protection tools exist. The question is whether your organization has implemented them.
Political Website Security During High-Visibility Moments

Advocacy organizations have predictable high-stakes moments: legislative votes, fundraising campaigns, media events, and public actions. These are also the moments when adversaries are most motivated to attack. A pre-event security posture review ensures defenses are ready before the moment arrives.
Political campaign website security gets tested hardest in exactly these windows. We learned this through direct experience. I was sitting at a cafe on a Sunday morning, scrolling through social media, when I saw that Donald Trump had decided to attack Club for Growth publicly. When a president mentions your client by name, you know the attention is coming. We immediately had to monitor the servers and make sure everything held up. The traffic was coming whether we were ready or not, and so were the attacks.
The Pre-Event Security Review
Two to four weeks before a high-stakes event, the infrastructure review should happen:
- Verify DDoS mitigation is active and configured
- Review WAF rules for current threats
- Confirm hosting can handle expected traffic surges
- Test backup and restore procedures
One to two weeks out, conduct an access audit:
- Review all WordPress admin and editor accounts
- Remove access for former staff, contractors, or volunteers
- Verify MFA is active on every account
- Reset passwords for all privileged accounts
In the final week:
- Document the current site state
- Enable file integrity monitoring
- Update all software
- Confirm that incident response contacts are current and available
The Campaign Website Security Calendar
Campaign website security reviews should map to the organizational calendar:
- Legislative votes and hearings. Full posture reviews with two to four weeks of lead time.
- Fundraising campaigns. Payment processing verification and capacity testing two weeks out.
- Report releases. Content integrity verification and backup checks.
- Year-end giving season. Full security review starting four weeks in advance, when donation volume peaks and attacker interest is high.
The pattern is consistent: if you can predict when your organization will be in the spotlight, you can prepare your defenses before the spotlight arrives. The organizations that get hurt are the ones that try to address security during a crisis rather than before one.
Incident Response: Planning for When, Not If
Organizations with incident response plans in place save an average of $1.5 million when a breach occurs. But for advocacy organizations, the stakes go beyond cost. A defacement detected and reversed in 10 minutes causes minimal reputational harm. One that persists for 24 hours gets screenshotted, shared on social media, and covered by news outlets. Response speed determines damage.
An advocacy incident response plan needs:
- Defined roles. Who leads the technical response, who manages external communications, who contacts legal counsel, and who notifies the board?
- Secure communication channels that don't depend on compromised systems
- Pre-drafted holding statements for common incident types, because crafting messaging during a crisis wastes critical time
- Regular testing. Tabletop exercises, where the team walks through a simulated incident at least quarterly, reveal gaps before a real incident exposes them.
The question is never whether your organization will face a security incident. It's whether you'll be ready when it happens.
What Your Organization Can Handle Internally vs. What Needs Professional Management
Internal Security Measures
Some security measures are straightforward enough for any organization to implement:
- Enforcing MFA on all WordPress accounts (99.9% effective at preventing credential stuffing attacks)
- Using a password manager and requiring unique passwords for organizational accounts
- Keeping WordPress core, plugins, and themes updated
- Maintaining regular backups
- Removing access for former staff immediately upon departure
- Limiting login attempts to block brute-force and credential stuffing
- Disabling XML-RPC if not actively used (it's a common attack vector)
- Changing the default
/wp-adminand/wp-login.phpURLs to reduce automated targeting
Where Professional Management Matters
Other measures require expertise and ongoing attention that most advocacy organizations can't realistically provide internally:
- Configuring and tuning WAF rules for your specific traffic patterns and threat profile
- Monitoring for and responding to active DDoS attacks
- Managing security posture escalation during high-visibility campaign periods
- Conducting pre-event security reviews
- Performing forensic analysis after incidents
- Coordinating incident response across technical, communications, and legal teams
The honest assessment: if your organization faces targeted attacks or operates in a space where they're a realistic possibility, self-managed security tools aren't enough. The tools themselves are available, many for free. But configuring them correctly, monitoring them continuously, and responding to incidents in real time requires expertise that most advocacy organizations don't have on staff and shouldn't try to build.
This is where working with a team with specific experience in protecting advocacy websites matters. Not a generic hosting company, not a general-purpose security firm, but a partner who understands the threats advocacy organizations face and has actually defended sites against politically motivated attacks. We cover why advocacy organizations, PACs, and campaigns trust FatLab for hosting and security in a dedicated article.
For organizations in the advocacy, political, or issue-campaign space, we cover what working with FatLab looks like on our advocacy and policy organization services page. For the broader context of how advocacy work shapes every aspect of web infrastructure, our hub article on WordPress for advocacy organizations covers the full picture, from rapid response readiness to donation infrastructure to the security dimensions discussed here.
If you're evaluating your organization's security posture, the WordPress security threats overview provides additional technical context on common attack vectors. Our coverage of hosting for advocacy and campaign sites addresses the infrastructure foundation on which security depends.
Advocacy website security isn't a one-time project. It's an ongoing posture that evolves as the threats against you change. The protection is available. The question is whether it's in place before the moment arrives when you need it.
