If visitors are telling you that your website is sending them to a gambling site, a fake pharmacy, or a page full of malware warnings, you're likely dealing with a WordPress redirect hack. And if you checked your site yourself and everything looked fine, that doesn't mean they're wrong.
Redirect hacks are one of the most disruptive WordPress infections because they're specifically designed to be invisible to you while actively harming every visitor who finds you through Google. Your site looks normal when you type in the URL directly. It looks normal when you're logged in as an admin.
But when a first-time visitor clicks through from a search result on their phone, they get sent somewhere else entirely.
This is one of the most common WordPress security threats we see on sites that come to us for help, and it's among the most damaging from a business perspective. A WordPress site redirecting to spam destroys visitor trust immediately, and the Google blacklisting that often follows can set your SEO back months.
What a WordPress Redirect Hack Actually Does
A WordPress redirect hack is malware that injects hidden code into your website's files or database, causing visitors to be automatically sent to attacker-controlled spam or scam pages. The redirect is conditional, targeting specific visitors based on criteria like device type, referral source, or login status while remaining invisible to site administrators.
The infection can live in multiple places: your .htaccess file, your wp-config.php, WordPress core files like wp-includes/version.php and wp-blog-header.php, theme files like header.php and functions.php, your database, or even fake plugins that attackers create and activate on your site.
Typical redirect destinations include pharmacy spam pages, fake dating sites, gambling portals, crypto scams, malware download pages, and phishing forms.
What makes this so damaging is the scale. Security firms observed over 500,000 websites infected with various types of malware in 2024, and over 60% of those were WordPress sites specifically carrying redirect malware.
The DollyWay campaign, documented by GoDaddy's security team in 2025, compromised over 20,000 WordPress sites and generated 10 million fraudulent impressions per month by routing visitors through a traffic direction system connected to the VexTrio cybercrime network, one of the largest known operations of its kind.
These aren't small, isolated incidents. Redirect hacks are an industry.
Why You Can't See It But Your Visitors Can
This is the part that trips up most site owners. You check your site, everything looks fine, and you conclude that the person complaining must be mistaken. But redirect hacks are engineered to avoid detection by the one person most likely to check: you.
How the WordPress Malicious Redirect Stays Hidden
Modern redirect malware uses conditional targeting, meaning it only redirects certain visitors under specific circumstances. Every WordPress malicious redirect variant we've encountered uses at least two of these techniques simultaneously.
| Technique | What It Does | Why You Miss It |
|---|---|---|
| First-visit only | Redirects new visitors, not returning ones | You've visited before so you see the normal site |
| Logged-in user exclusion | Skips admin/editor accounts | Site looks fine when you're logged in |
| Search engine referral only | Only redirects visitors from Google | Direct visits work normally |
| Geographic targeting | Redirects visitors from specific countries | Your location may not be targeted |
| Device targeting | Redirects only mobile or desktop | You may be checking on the wrong device |
Logged-in user exclusion is the most common evasion technique. WordPress admin users never see the redirect. Only logged-out visitors, your actual audience, get redirected. You literally can't see the problem while logged into your dashboard.
Search engine referrer targeting means the malware checks where the visitor came from. If they arrived from Google, Bing, or Yahoo, they get redirected. If you typed the URL directly into your browser, you see the normal site.
First-visit cookie targeting sets a cookie on the initial visit and only redirects once. If you visit again, you see your normal site. This makes reproduction difficult, and it's why "I checked, and it looks fine to me" is the most common response from site owners dealing with an active infection.
Mobile-only targeting is another common variant. Some infections specifically target mobile devices while skipping desktop browsers, since site owners typically test on desktop.
IP-based filtering can exclude IP ranges associated with hosting providers and security companies. Some variants even learn the site owner's IP address and skip it entirely.
"Zero redirect attacks and zero pharma attacks in FatLab's history. I attribute that directly to our mandatory WAF policy."
All of these techniques combined mean a WordPress redirect hack can run for weeks or months before anyone on your team notices. Usually, the first sign is a complaint from a visitor, a warning from Google Search Console, or your hosting provider flagging the account.
Where the Malicious Code Hides
Redirect malware doesn't live in just one place. That's what makes cleanup difficult. Miss one injection point, and the site reinfects itself within hours.
Server Configuration Files
The .htaccess file is the most common injection point because it operates at the Apache server level, before WordPress even loads. A clean WordPress .htaccess file is about 10 lines long. If yours contains RewriteCond rules that check for search-engine referrers or mobile user agents, and RewriteRule directives that point to external domains, it's been compromised.
Attackers also inject malicious require, include, or eval statements into wp-config.php because it loads on every WordPress request. These often pull in remote malware files or execute obfuscated redirect code through eval(base64_decode(...)) calls.
WordPress Core Files
Some variants modify WordPress core files directly. Common targets include wp-includes/version.php, which loads early in the WordPress boot process, wp-blog-header.php, which serves as the entry point for all frontend requests, and wp-load.php, which loads the WordPress environment.
Attackers also append malicious code to JavaScript files in wp-includes/js/, piggybacking on legitimate jQuery files. Core file integrity checks compare file hashes against WordPress.org originals and catch these quickly, but only if you're running them.
Theme and Plugin Files
Theme files like header.php, footer.php, and functions.php are favorite targets because they execute on every page load. The malicious code is typically obfuscated using base64_decode(), str_rot13(), or gzinflate() encoding, with variable names designed to resemble legitimate WordPress functions.
Attackers also create entirely fake plugins in your /wp-content/plugins/ directory with innocent-sounding names like wp-performance-optimizer or cache-manager-plus. These get activated and load on every request. The DollyWay campaign specifically installed a modified version of the WPCode plugin that contained obfuscated malware snippets.
Database Injections
Malicious JavaScript or iframes can be injected directly into your wp_posts table, your widget content in wp_options, or your theme settings. Database injections are harder to detect manually because the malicious code is stored as serialized data mixed in with your legitimate content.
In some cases, attackers change your siteurl or home options in wp_options to redirect the entire site. They also create hidden administrator accounts in wp_users for persistent access.
The Uploads Directory
Attackers place PHP files disguised with innocent names in /wp-content/uploads/, a directory that should contain only images, PDFs, and other media files. Files named things like social-icons.php or thumb-handler.php blend in with legitimate upload handling, but they're backdoors that enable reinfection even after a partial cleanup.
How Redirect Hacks Get In
Understanding the entry vector matters because cleaning up a redirect hack without addressing how it got in guarantees reinfection.
Vulnerable plugins and themes are the primary entry vector. The WordPress ecosystem sees roughly 22 new vulnerabilities per day. Outdated plugins with known security flaws are the easiest path in for automated scanning bots, and those bots are scanning constantly. The risk is compounded when trusted plugins are compromised at the source, delivering malware through normal update channels.
"You don't have to be on anyone's threat list. You don't have to be a target. You don't have to be controversial."
Bots scan IP ranges looking for any site running a vulnerable version of a popular plugin. Your organization's profile, your content, your audience: none of it matters to an automated scanner.
Compromised credentials are the second most common vector. Weak passwords, reused passwords, or credentials leaked in other breaches give attackers direct admin access without needing to exploit any vulnerability. Brute force attacks and user enumeration automate this process, making credential compromise a matter of when, not if, for sites without proper authentication hardening. Once they're in, a redirect hack is just a matter of time.
Insecure hosting environments also play a role. On shared hosting without proper account isolation, a compromised site on the server can spread infections to neighboring accounts. PHP execution enabled in the uploads directory, outdated server software, and missing file permission controls all widen the attack surface.
This is why we take a prevention-first approach to security. The redirect hack itself is the symptom. The root cause is almost always a gap in one of these three areas.
Business Impact Beyond the Redirect
The redirect itself is damaging enough. Your visitors are being sent to scam sites, and your organization's reputation takes a hit every time it happens. But the downstream consequences are often worse than the infection itself.
Google Blacklisting
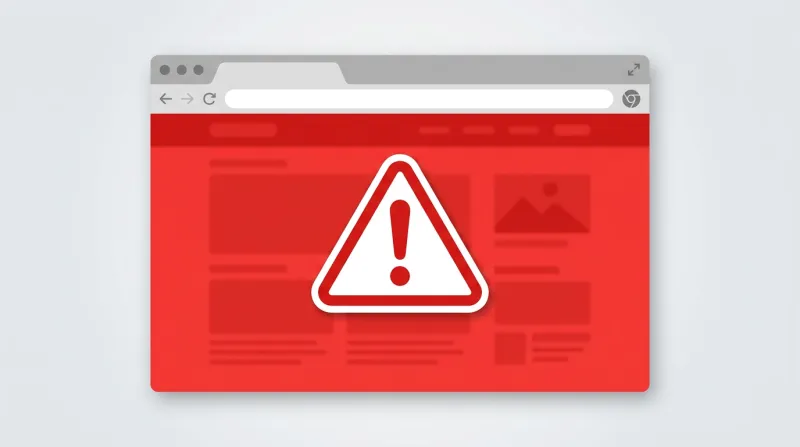
When Google detects a redirect hack, it can flag your site with warnings like "This site may be hacked" in search results or display a full-page "Deceptive site ahead" interstitial in Chrome. Since Chrome, Firefox, and Safari all use Google Safe Browsing data, the warning appears across browsers.
The impact on traffic is immediate and severe. Organic traffic typically drops 80-95% once a blacklist warning is active, and the warning doesn't disappear the moment you clean the infection.
| Scenario | Expected Timeline | Conditions |
|---|---|---|
| Best case | 5-7 days | Clean removal, immediate reconsideration request |
| Typical | 10-14 days | Some remnants found on first review |
| Worst case | 3-4 weeks | Reinfection or incomplete cleanup |
| SEO recovery | 30-90 days | Rebuilding organic rankings after deindexing |
Even after the warning is removed, rankings may not return to pre-hack levels for months. Some lost backlinks never recover if linking sites removed their links after seeing the warning.
"It's not a wait-and-see game where you clean up afterwards. It's a multi-layer approach to keeping it from happening in the first place. And then if it does happen, acting insanely fast so you don't end up blacklisted."
Reputation and Trust
For nonprofits, associations, and advocacy organizations, the damage to trust can be harder to quantify but just as real. Members or supporters who encounter a redirect to a scam site may not come back. Even after the infection is cleaned, the experience lingers.
How to Fix a WordPress Redirect Hack
My position on this is clear: use professional services for hack cleanup, not DIY. If you need to fix a WordPress redirect hack, doing it properly is the difference between a one-time cleanup and a recurring nightmare.
"Infections are self-replicating. They compromise both files and the database. To think you're going to clean it up manually is a gamble."
The reason is straightforward. Redirect hacks install multiple infection points and backdoors across your files and database. If you find and remove the obvious redirect in your .htaccess file but miss the backdoor in your uploads directory and the hidden admin account in your database, the site reinfects itself from the pieces you missed.
The DollyWay campaign specifically included an auto-reinfection mechanism that spread PHP code across all active plugins, re-injecting itself on every page load.
We use Sucuri for professional cleanup. We've had a relationship with them for over 10 years. Their scanning technology is designed to find every piece of an infection across files, the database, and server configuration.
In 2023, 58,848 WordPress sites with Wordfence installed were still infected, and in 14% of cases, redirect malware tampered with Wordfence's own files to stay hidden. That's the limitation of plugin-level security: if the malware can modify the plugin itself, the plugin can't protect you. It's one of the reasons we rely on server-level scanning with Imunify360, which operates entirely below WordPress and can't be tampered with by WordPress-level malware.
The cleanup process follows a systematic approach:
- Take the site offline to stop harm to visitors
- Back up the infected site for forensic analysis
- Replace all WordPress core files with fresh copies
- Reinstall plugins from scratch rather than trying to clean them
- Audit theme files and the database for injected code
- Remove unauthorized admin accounts
- Verify the cleanup from multiple angles, including testing with mobile user agents and search engine referrers, not just checking the site while logged in
After cleanup, the hardening steps matter just as much: updating everything, removing unused plugins and themes, regenerating security keys, setting proper file permissions, and disabling file editing through the WordPress admin. Without these steps, the same vulnerability that let attackers in the first place remains open.
For a detailed look at how we handle recovery from start to finish, see our guide on WordPress hack recovery.
The Overlap With Pharma Hacks
Redirect hacks and pharma hacks frequently co-occur. Many infections involve both redirect behavior and SEO spam injection. The same compromised access point that enables a redirect can also be used to inject pharmaceutical keywords and links into your content, specifically targeting search engine crawlers.
If your site has a redirect hack, it's worth checking for pharma spam as well. A site redirecting visitors to spam is often just the visible layer of a deeper infection. The cleanup process needs to address both, or you'll end up with a second round of Google Search Console warnings after you think the problem is solved.
How We Prevent This for Our Clients
We have zero redirect attacks and zero pharma attacks across FatLab's entire history. That's not luck. It's architecture.
Our defense starts at the edge with Cloudflare Enterprise WAF, filtering all traffic before it reaches the server. This is non-negotiable for every site we host. The WAF blocks known attack patterns, malicious bot traffic, and exploitation attempts for known vulnerabilities, often before a software patch is even released.
At the server level, Imunify360 provides real-time malware scanning that catches file modifications within minutes. If an attacker somehow gets code onto the server, Imunify360 detects and quarantines it before any visitor is affected. This is a server-level protection that plugins can't replicate because it operates entirely below WordPress.
On top of that, we run weekly updates across our entire fleet to close the vulnerability window that attackers exploit. Outdated plugins are the number one entry vector for redirect hacks, and our automated update system keeps that window as narrow as possible. When high-severity vulnerabilities are disclosed, we patch outside the regular schedule.
Daily backups with 30-day retention mean that even in a worst-case scenario, we can quickly restore to a known clean state. And 24/7 monitoring catches anomalies that automated systems might miss.
"Security is not an option. Anyone who guarantees you 100% security is a fool. What we guarantee is that we have the best tools, practices, and services in place, plus rapid response and recovery."
The difference between a site that gets redirect-hacked and one that doesn't usually comes down to whether someone is actively maintaining the security infrastructure or whether the site is just sitting there with an outdated plugin and no WAF. For organizations that want to make sure their WordPress site isn't redirecting to spam or scam pages, our WordPress security services cover the full stack: edge protection, server-level scanning, proactive updates, and incident response.
You can also read about why organizations choose FatLab for WordPress security and how our approach compares to plugin-only solutions.
What to Do Right Now
If you're reading this because your site is actively redirecting visitors, here are the immediate priorities:
- Don't try to fix it yourself by editing individual files. You'll likely miss injection points, and the infection will return.
- Take the site offline with a maintenance page to stop visitors from being redirected to malicious content.
- Change all passwords immediately. WordPress admin, FTP/SFTP, hosting panel, and database.
- Check Google Search Console for security warnings. If your site is flagged, you'll need to submit a reconsideration request after cleanup.
- Contact a professional cleanup service. Whether that's us, Sucuri, or another qualified team, this isn't a job for manual file scanning.
If you want to check whether your site has been compromised, scanning tools like Sucuri SiteCheck can detect client-side redirect malware. But keep in mind that server-side redirects and .htaccess redirects are invisible to remote scanners because the scanner's request doesn't match the conditional targeting criteria. A clean remote scan doesn't guarantee a clean site.
Frequently Asked Questions
Why can't I see the redirect on my own site?
Redirect hacks are built to avoid detection by site owners. The malware checks whether you're logged in, whether you've visited before, what device you're using, and where you came from. If you're an admin browsing from your usual computer, you'll see the normal site every time. The redirect only fires for new visitors, often only those coming from Google on a mobile device. That's why the first sign is usually a complaint from someone else.
Will Google blacklist my site for a redirect hack?
It can, and that's one of the biggest risks. When Google detects that your site is sending visitors to spam or malware pages, it can flag your site with a "Deceptive site ahead" warning in Chrome, Firefox, and Safari. Organic traffic drops 80 to 95 percent almost immediately. The warning doesn't go away the moment you clean the infection either. You need to submit a reconsideration request through Google Search Console, and the review process takes anywhere from a few days to a few weeks.
How do I fix a WordPress redirect hack?
The honest answer is to use a professional cleanup service rather than trying to do it yourself. Redirect hacks install multiple infection points across your files, database, and server configuration, along with backdoors that reinfect the site if you miss even one. We use Sucuri for cleanup because their tools are designed to find every piece of an infection. After cleanup, you need to close the entry point by updating all plugins, changing all passwords, and putting proper security infrastructure in place.
Can a security plugin prevent redirect hacks?
A plugin alone isn't enough. Plugin-level security tools run inside WordPress, which means the malware can sometimes tamper with the plugin itself. We've seen cases where redirect malware modified Wordfence's own files to stay hidden. A web application firewall running at the network edge, like Cloudflare, is far more effective because it blocks attack patterns before they reach your server. Server-level scanning with tools like Imunify360 adds another layer that operates completely outside WordPress.
How do redirect hacks get onto my site in the first place?
The two most common entry points are outdated plugins and compromised credentials. Bots scan the internet constantly looking for WordPress sites running plugins with known vulnerabilities. When they find one, the exploit and malware deployment happen automatically. Weak or reused passwords are the second biggest vector, especially when combined with no two-factor authentication. In shared hosting environments, one infected account on the server can sometimes spread to others.
The fastest path from "my site is redirecting" to "my site is clean and protected" runs through professional cleanup followed by proper hosting and maintenance infrastructure. The WordPress redirect hack is the symptom. Ongoing security management is the cure.
