What's the best WordPress security plugin? That's the wrong question to start with, and I'll explain why.
I just spoke with a potential client yesterday, a nationally recognized medical association. They discovered embarrassing advertisements had been injected into their professional website.
The ads had been running for approximately two weeks before they caught it themselves.
Here's the uncomfortable part: they had a WordPress security plugin installed. It didn't catch this.
This is the reality of plugin-based WordPress security. The plugin was there, the client felt protected, and meanwhile, their professional medical site was serving ads to members and the public for two weeks.
This isn't about blaming a single plugin or situation. It's about understanding a fundamental limitation: security plugins alone create a false sense of protection.
For organizations handling mission-critical information, such as associations, nonprofits, and professional services, false security is worse than no security at all.
How WordPress Security Solutions Actually Work

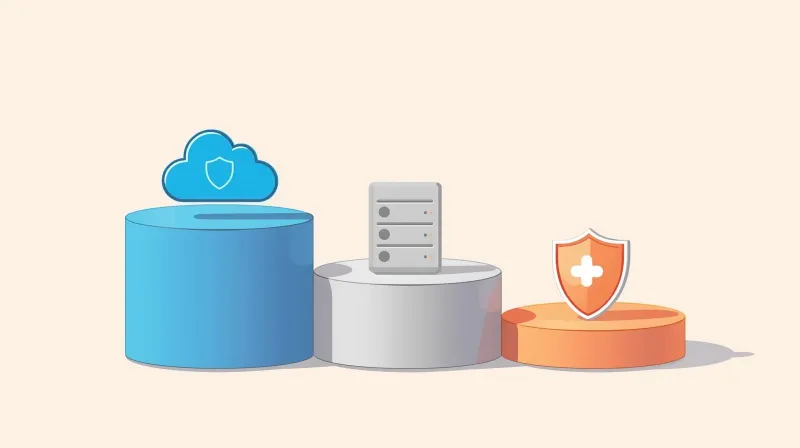
WordPress security isn't a single-layer problem. It works in three distinct layers, each operating at a different point in the threat defense chain. Understanding these layers is essential before choosing any WordPress security plugin or service.
Layer 1: Edge/Cloud Level
Examples include Cloudflare WAF and Sucuri firewall service.
This stops threats before they reach your server. This is where you want protection.
Layer 2: Server Level
Examples include Imunify360, BitNinja, and ConfigServer Firewall.
This operates below WordPress at the hosting infrastructure level. It catches what gets past the edge.
Layer 3: Application Level
Examples include Wordfence, Sucuri plugin, and MalCare.
This runs inside WordPress itself. It's the last line of defense, and the weakest.
The Problem
Most people install a plugin and assume they're covered.
But they're only addressing Layer 3, the level where threats have already reached your server and are knocking at your door.
Why WordPress Security Plugins Fall Short

Security plugins have a fundamental architectural limitation: they're reactive, not proactive.
The attack has to hit your server before the plugin can respond.
Here's what that means in practice.
The Reactive Protection Problem
Plugins like Wordfence implement basic security measures, such as IP logging. If an IP address hits your site too many times, especially the admin area, the plugin blocks traffic.
We've seen clients contact us after installing Wordfence, only to find they're locked out of their own admin area.
A bot repeatedly hit the login screen, and the plugin's response was to lock everything down. The protection mechanism itself created the outage.
This is reactive security. It waits for the attack, then responds.
Compare this to edge-level protection at Cloudflare, which analyzes traffic patterns across millions of sites globally and stops threats before they ever reach your server.
Database Bloat Can Crash Your Site
Security plugins do extensive logging. They log IP hits, admin form attempts, and geographic lookups.
On shared hosting plans with limited resources, we've seen the database storage fill up completely.
The plugin meant to protect the site actually crashes it.
Under a sustained bot attack, those log files grow fast. Though each entry is small, the cumulative effect on a limited hosting plan can bring a website down.
Finite storage space. Unlimited attack attempts. You can see the vulnerability.
Plugins Can Contribute to DDoS Attacks
In a weird twist, security plugins can actually contribute to distributed denial-of-service attacks.
When a website is under attack, these plugins consume CPU and RAM as they try to log every attempt, run geographic lookups, and update local threat databases.
On resource-constrained hosting, the plugin itself eats up all available processing power.
The plugin meant to defend against the attack becomes part of the problem.
Threat Databases Are Always Out of Date
When you log into many security plugins, you'll see a notification: "Your threat database needs updating."
If the threat database is stored locally or partially locally, your website's protection is only as current as the last update. Your site only knows about threats it's personally seen or threats documented in its last database refresh.
Meanwhile, edge-level protection, such as Cloudflare Enterprise, processes the world's internet traffic in real time.
When a new attack vector emerges anywhere in the world, Cloudflare's systems, now enhanced with AI, identify, analyze, and patch it incredibly quickly.
A plugin's environment is literally just your website. That's all it knows.
The difference in scope and response time is massive.
The Budget Host Security Theater
This plugin problem is amplified by how budget hosting companies sell security.
GoDaddy and Bluehost are very good at using the word "managed." But managed in their context means they manage their servers, not your website.
If you have any security concerns, they don't consider it an emergency. They consider it an upsell opportunity.
After navigating tiered support and long hold times, you'll be sold SiteLock or a similar add-on service. No comprehensive security is included in your plan; only opportunities to purchase additional services.
The SiteLock Configuration Problem
Here's what we've seen repeatedly: clients migrate to us from GoDaddy, who thought they had protection because they bought SiteLock.
It showed up as a line item on their monthly bill.
But it was never actually configured for their website.
Maybe DNS record changes were required. Maybe a plugin needed to be installed to connect to the system. Maybe they just sold the license, and the client needed to activate it.
These are technical steps that non-technical website owners don't know how to handle.
They paid for security. They didn't get security.
Because buying a subscription isn't the same as having managed protection.
The Timing Problem
Often, what happens is this:
- Clients buy the cheap hosting plan
- They encounter a security concern
- They call support and get upsold to SiteLock
The problem is that SiteLock isn't in place until you've purchased it. And you're not going to purchase it until you have a security concern, which may already be too late.
If your site is under attack from a DDoS, it's probably been that way for a while before you noticed. If you've been hit with malware, cleanup could cost hundreds of dollars even with a security service.
All this stuff needs to be in place from day one. Proactive, not reactive.
FatLab's Security Approach

At FatLab, we insist on hosting and managing the websites we support.
It's not a business preference. It's a technical requirement.
We can't be responsible for security unless we control the entire environment. If we don't have full control over the server and security stacks, we can't provide any level of confidence in protection.
What's in Place for Every FatLab-Hosted Site
Cloudflare Enterprise WAF
First line of defense at the DNS level. All traffic passes through Cloudflare's firewall before reaching our networks.
It cleans the entire way using global threat intelligence gathered from processing a substantial portion of the world's internet traffic.
Imunify360
Server-level security operating below WordPress. Real-time malware scanning with automatic cleanup.
Proactive defense mechanisms that stop threats before they affect your website.
Isolated Server Applications
No neighbor-to-neighbor threats.
Your website isn't vulnerable because someone else on the same server got hacked.
24/7/365 Monitoring
From multiple geographic locations with immediate alerts.
We find problems before clients do.
SafeUpdates Process
Weekly automated updates with full testing in a virtual environment first. Visual regression testing compares screenshots for anomalies.
Critical updates are applied immediately when made public. If anomalies are detected, updates are blocked, and our team investigates.
30-Day Backup Retention
Multiple layers, both on-site and off-site storage.
The Message to Clients
You don't need security plugins with us.
You don't need subscriptions to Jetpack's firewall or Sucuri's WAF. You don't need your own Cloudflare account.
We handle that.
What We Do With Existing Security Plugins
When we migrate a site that's already using Wordfence or similar plugins, we disable them immediately during the migration process.
Eventually, we remove them entirely. They're not needed on our platform, and they add unnecessary overhead, storage consumption, and database bloat.
Security plugins are notorious for leaving behind junk after uninstall.
Wordfence, for example, leaves its database tables intact. They're probably trying to be helpful in case you reactivate or reinstall.
What we end up doing is scrubbing the database and removing those bloated tables, which improves performance.
When WordPress Security Plugins Make Sense
A security plugin is absolutely better than nothing.
If you're on shared hosting and can't move to managed hosting immediately, yes, go ahead and use a plugin. Some security is better than no security.
But not all security services are equal.
Here's what I'd recommend in order of preference:
Option 1: Cloudflare Free Tier (Best)
Cloudflare offers a free tier that provides massive security advantages.
It requires some technical knowledge. You'll need to change your DNS records from pointing at your web host to pointing at Cloudflare services.
This alone stops the vast majority of threats at the edge before they reach your server.
It's free, and it's dramatically better than any plugin-based approach.
Option 2: Sucuri Security Service ($200-300/year)
Sucuri provides a cloud-based firewall plus malware scanning.
It requires DNS record changes and some configuration, but it's worth it. It's not as comprehensive as what we provide at FatLab, but it's good security.
This is a service, not just a plugin. That distinction matters.
Option 3: Security Plugins (Last Resort)
If Cloudflare or Sucuri aren't in your budget or your technical comfort zone, consider plugins. If you're searching for the best security plugin for WordPress as a standalone solution, here are the options worth considering.
Wordfence
Offers a WAF in addition to plugin-level security, making it relatively comprehensive for a plugin-based solution. Read our full Wordfence review for an honest assessment.
Just be aware of the database bloat and resource consumption issues we discussed. If you're considering the paid version, see our Wordfence Free vs Premium comparison.
Jetpack
Made by Automattic, the company behind WordPress. That credibility matters.
They offer firewall services along with website-level security.
Use these with full awareness of their limitations. They're a last resort, not a complete solution.
The Real Security Mistake
The most common security mistake we see isn't choosing the wrong plugin.
It's making two fundamental assumptions:
Assumption 1: Security Is Included in Hosting
Many hosts do not provide comprehensive security. That's a fact.
You may need to self-manage it, or it may be sold as an upsell or additional service you need to configure yourself.
I understand why people assume security is included. Honestly, it should be. That's why we include it at FatLab.
But assuming all hosting includes it is a costly mistake.
Assumption 2: A Plugin Is Enough
These plugins claim to secure your website. You install them, and you're done, right?
That's the mistake.
Security is not plug, play, forget. Especially not for organizations handling mission-critical information, conducting important transactions with members, constituents, donors, and volunteers.
A plugin might be part of a security strategy. It should never be the entire strategy.
What to Do Right Now
If you're currently relying only on a security plugin, here's what to evaluate:
Can You Move to Better Hosting?
Look for managed WordPress hosting that includes server-level security and proactive monitoring.
This solves the problem at the infrastructure level.
Can You Add Edge-Level Protection?
Even if you can't change hosts immediately, adding Cloudflare (free tier) or Sucuri's firewall service dramatically improves your security posture.
Are You on a Budget Host With Security Concerns?
Be very careful about security upsells.
Understand exactly what you're buying and whether you have the technical knowledge to configure it properly. Paying for SiteLock doesn't mean you have security. It means you have a subscription that needs to be set up.
Do You Manage Mission-Critical Information?
If your organization holds sensitive data, processes transactions, or would face serious consequences from a security breach, plugin-based security isn't sufficient.
You need managed, enterprise-grade protection.
Our Recommendation
Instead of asking "what's the best WordPress security plugin," ask "what security infrastructure do I need?"
The answer for most organizations is comprehensive, professionally managed security operating at the cloud and server level. Not a plugin you install and hope works.
At FatLab, we've built our entire hosting and support service around this principle. Fully comprehensive, enterprise-grade security that's managed for you, not something you need to configure, update, and monitor yourself.
If you're on shared hosting and need immediate protection, start with Cloudflare's free tier.
If you have a few hundred dollars in your annual budget, add Sucuri's service.
If neither is feasible right now, use Wordfence or Jetpack with full awareness of their limitations.
But understand that plugins alone are security theater. Real protection happens at the infrastructure level, before threats reach your WordPress installation.
That medical association I mentioned? They're evaluating moving to properly managed hosting.
Not because they chose the wrong plugin, but because they've learned that plugins can't solve an infrastructure problem.
Related Security Plugin Guides
If you're researching specific plugins or need help deciding between options, these detailed guides may help:
Plugin Reviews:
- Wordfence Review: The most popular security plugin analyzed
- Sucuri Review: Free plugin vs paid firewall service explained
- MalCare Review: The "set and forget" approach evaluated
- All In One WP Security Review: The free alternative worth knowing
- Solid Security (iThemes) Review: What changed with the rebrand
Comparisons:
- Wordfence vs Sucuri: Plugin-based vs cloud-based protection
- Wordfence vs MalCare: Control vs simplicity
- Wordfence Free vs Premium: Is $149/year worth it?
- Wordfence Alternatives: Options if Wordfence isn't right for you
Conceptual Guides:
- Do You Need a Security Plugin?: Decision framework based on your hosting
- Security Plugins vs Server-Level Protection: Understanding the layers
- Sucuri Plugin vs Sucuri Service: What you actually get at each price
- Why SiteLock Upsells Fail: The budget hosting security trap
