Most WordPress security discussions focus on plugins such as Wordfence, Sucuri, MalCare, and others. But plugins represent just one layer of security, and not the most important one.
Server-level protection operates below WordPress. It catches threats that plugins never see and continues working even when WordPress is compromised.
Understanding this distinction fundamentally changes how you should think about WordPress security.
The Security Layer Model

WordPress security works in three distinct layers. Each operates at a different level of your infrastructure.
Layer 1: Edge/Cloud Level
Examples: Cloudflare WAF, Sucuri Firewall Service
This is protection at the network edge, before traffic reaches your server. DNS traffic passes through the security service, which filters malicious requests before they reach your infrastructure.
What it catches:
- DDoS attacks
- Known malicious IP addresses
- Common attack patterns
- Bot traffic
Why it matters: Threats never reach your server. Your infrastructure isn't burdened by processing attacks.
"By taking advantage of Cloudflare WAF, you're taking advantage of the world's internet traffic and what Cloudflare Enterprise has studied and seen. Even when a new attack vector hits the internet, Cloudflare has likely already seen it and knows how to deal with it, especially with their new AI systems in place. They can identify, rectify, and patch insanely quickly at a global scale, whereas your plugin's environment is literally just your website. And that's all it knows, plus the latest threat database that the plugin is using. Just by sheer size and data, the Enterprise Firewall that operates at the edge is going to be massively better."
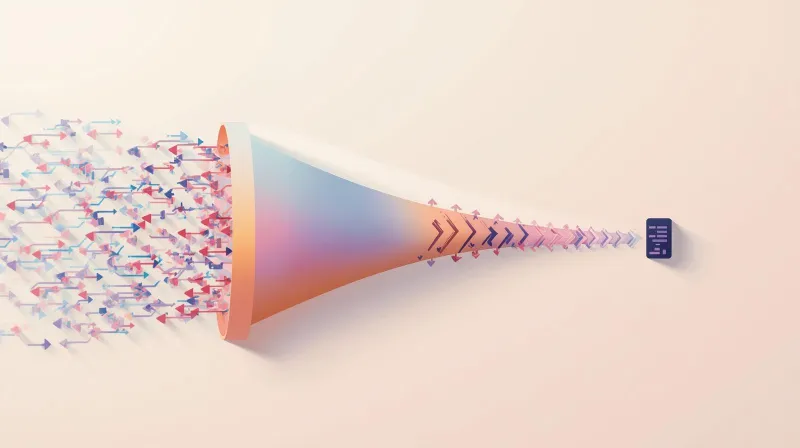
Layer 2: Server Level
Examples: Imunify360, BitNinja, ConfigServer Firewall
This is protection at the operating system level, below WordPress, but on your server. It monitors files, processes, and network activity at the server layer.
What it catches:
- Malware before it affects WordPress
- Server-level intrusions
- Compromised files regardless of application
- Threats that bypass edge protection
Why it matters: This layer continues to function even if WordPress is compromised. If an attacker gains access to WordPress, server-level protection still works.
Layer 3: Application Level
Examples: Wordfence, MalCare, Solid Security
This is protection inside WordPress. Plugins run within the WordPress environment, analyzing traffic and files at the application level.
What it catches:
- WordPress-specific vulnerabilities
- Plugin and theme exploits
- Brute force login attempts
- File modifications within WordPress
The fundamental limitation:
"Plugins have a major fault. Though I know some of them do, for an additional fee, provide a WAF, many security plugins rely on the attack hitting the server before they kick in. That means the threat is already knocking at your door. I find this to be very scary in and of itself."
This layer depends on WordPress functioning. If WordPress is compromised at a fundamental level, plugin-based security may not work either. And critically, plugins must be updated: they're only as good as their last update. Even with a diligent weekly update plan, your site is potentially not up to date on the latest security threats for six days a week. These things change by the day, if not by the hour.
Security Layer Comparison
| Capability | Edge Level (Cloudflare) | Server Level (Imunify360) | Application Level (Plugins) |
|---|---|---|---|
| DDoS Protection | ✓ Full protection | Partial | ✗ Cannot protect |
| Blocks before server impact | ✓ Yes | Partial (on server) | ✗ No |
| Malware scanning | ✗ No | ✓ Real-time | ✓ Scheduled |
| WordPress-specific hardening | ✗ No | Partial (WAF rules) | ✓ Full |
| Works if WordPress compromised | ✓ Yes | ✓ Yes | ✗ No |
| Resource impact on site | None | Minimal | High during scans |
| Global threat intelligence | ✓ Massive dataset | ✓ Large dataset | Limited to plugin DB |
| 2FA for WordPress | ✗ No | ✗ No | ✓ Yes |
| Cost | Free tier available | Included with quality hosting | Free + Premium options |
Why the Distinction Matters
Plugins Can't Protect Against Server-Level Threats
A security plugin runs inside WordPress. It can only see what WordPress sees.
If an attacker exploits a server vulnerability, compromises another application on shared hosting, or gains access via a vector outside WordPress, your security plugin will know nothing about it.
Wordfence can't detect a compromised PHP process. MalCare can't see malware in your server's cron jobs. Solid Security can't block an attack targeting your server's SSH.
Server-level protection sees all of this.
Plugins Depend on WordPress Working
Here's a scenario: an attacker compromises your WordPress installation at a fundamental level, perhaps through a vulnerable plugin that grants file system access.
Your security plugin is now running in a compromised environment. The attacker can potentially disable it, modify its behavior, or bypass its checks entirely.
Server-level protection operates below this. Even if WordPress is fully compromised, Imunify360 continues to scan, detect, and clean malware at the file system level.
Resource Consumption
Plugins use your server's resources. When Wordfence runs a scan, it consumes CPU, memory, and I/O on your server. On resource-constrained hosting, this impacts performance.
Server-level tools like Imunify360 are optimized to run at the infrastructure layer with minimal impact on individual applications. They're designed for always-on protection without the overhead of application-level scanning.
Server-Level Protection: Imunify360
Imunify360 is the server-level security tool we use at FatLab. It's an all-in-one, automated security solution specifically designed for web hosting environments. Here's what it provides:
Advanced Firewall
The cloud-based system analyzes traffic and blocks suspicious connections to the server before they reach applications. It defends against brute-force, port-scanning, and DoS attacks at the server level, not the WordPress level.
Web Application Firewall (WAF)
Filters HTTP traffic between web applications and the internet. Prevents SQL injections and cross-site scripting (XSS) attacks. Includes tailored rule sets specifically for WordPress, Joomla, and Drupal.
Proactive Defense
Imunify360 doesn't just scan for known threats. It uses machine learning to identify suspicious behavior patterns across millions of sites globally. New attack vectors are detected based on behavior, not just signatures.
This matters because zero-day vulnerabilities don't have signatures. Traditional scanners miss them. Behavioral analysis catches them.
Weak Password Protection
This feature analyzes WordPress login attempts and checks passwords against a database of known weak passwords. If a weak password is detected, users are redirected to a password reset page. This prevents compromised credentials from ever logging in, something plugins handle reactively, if at all.
Real-Time Malware Scanning and Automatic Cleanup
Files are scanned continuously at the file system level. When malware appears, Imunify360 detects it immediately and can automatically clean it. No waiting for a scheduled scan. No manual intervention required.
The detection happens below WordPress. Even if an attacker tries to evade detection by manipulating WordPress, the file system scan still catches the malicious files. Real-time cleanup means malware is removed before it can spread, cause blacklisting, or harm your visitors.
Server-Wide Protection
Imunify360 protects the entire server, not just WordPress. If you have multiple applications, email services, or other components, they're all monitored. It even includes email spam protection that prevents your server from being used for unauthorized outgoing spam.
Plugins can only protect WordPress. Server-level tools protect everything.
Why This Is Superior to Plugins
Server-level security has key advantages over application-level plugins:
- Runs at server level (not application level)
- Real-time cleanup before issues affect your traffic or cause blacklists
- Always up to date with the latest threat data from global intelligence
- No local database bloat or resource consumption on individual sites
- Machine learning analyzes traffic patterns across millions of sites
- All features are enabled by default at no additional cost on our hosting
When Plugins Add Value
I'm not saying security plugins are useless. They have legitimate use cases.
Visibility
Plugins like Wordfence provide detailed visibility into attack attempts, login activity, and security events. Even with server-level protection, this visibility helps you understand the threats you face.
WordPress-Specific Hardening
Plugins can implement WordPress-specific security measures, such as login rate limiting, hiding the login URL, enforcing strong passwords, and two-factor authentication.
These features operate at the application level, where they make sense.
Defense in Depth
Multiple layers of protection catch what other layers miss. A threat that bypasses edge protection might be caught at the server level. Something that evades server scanning might be caught by an application-level plugin.
There's value in redundancy, as long as you understand what each layer provides.
When Plugins Create False Confidence
The problem isn't plugins themselves. It's when plugins are the only security layer.
"I Have Wordfence, So I'm Secure."
This is security theater. Wordfence provides real protection, but it can't defend against server-level threats and relies on WordPress functioning correctly.
If your hosting lacks server-level security and you rely entirely on Wordfence, you have significant gaps.
Database Bloat From Logging
Security plugins log extensively. IP addresses, attack attempts, geographic data, and even geo-lookups to determine where IPs are located. On resource-constrained hosting, this logging can fill up database storage.
"They do a ton of logging. They log IP hits. They log admin form attempts. They even do some geotagging. So, they look up a local database to determine where the IP address is from. With limited resources, the database storage and/or the hosting plan storage can fill up. We have rescued sites that have basically become so bloated with security logs that they come down."
You can see the vulnerability in logging on the host itself, because there's a finite amount of space. Though these log files are small, under a big bot attack, they can crash a website.
Resource Consumption During Attacks
During a sustained attack, plugins work harder: more logging, more scanning, more blocking. This consumes resources precisely when your server is already stressed.
"We have seen that web performance is hindered. A website is under attack. And due to all the processes, including the logging I just talked about, that these plugins do, they basically eat up all the CPU and RAM. Weirdly, they're actually contributing to a DDoS attack because they're filling up the server's resources, trying to log or combat some kind of bot attack."
In extreme cases, the plugin's response to the attack contributes to a denial-of-service attack. The security tool meant to defend against the attack becomes part of the problem.
The Right Approach
Security works best when layers complement each other rather than overlap.
Foundation: Server-Level Protection
Start with Imunify360 or a similar server-level security solution. This catches threats before they reach WordPress and continues working even if WordPress is compromised.
If your hosting doesn't include server-level protection, you're starting from a weak position. No amount of plugins compensates for this gap.
Enhancement: Edge-Level Protection
Add Cloudflare or another edge service. This stops threats before they reach your server, reducing load and catching attacks early.
The free Cloudflare tier provides significant protection. You don't need to spend money to add this layer.
Optional: Application-Level Plugins
With server and edge protection in place, application-level plugins become optional. They add visibility and WordPress-specific features but don't carry the primary security burden.
If you add a plugin, use it for what it's good at: visibility, hardening, WordPress-specific security features. Don't expect it to be your entire security strategy. (For help deciding if you need one, see do you need a WordPress security plugin?)
What This Means for Hosting Decisions
The hosting you choose determines what security layers are available.
Budget Shared Hosting
Typically provides minimal server-level security, no edge protection, and leaves you responsible for everything at the application level.
You're forced to rely on plugins because you have no other options. This is the weakest position.
Managed WordPress Hosting (Quality Providers)
Typically provides: server-level security (Imunify360 or similar), often includes edge protection (Cloudflare integration), and proper resource allocation.
Plugins become optional because the infrastructure provides real security. This is a much stronger position.
FatLab's Approach
Every site includes Cloudflare Enterprise WAF (edge-level) and Imunify360 (server-level). We also include isolated environments, continuous monitoring, and proactive updates. See our managed WordPress security services for the full picture.
Our clients don't need security plugins. The infrastructure handles it. If they want to add Wordfence for visibility, that's fine, but it's not carrying the security burden.
The Bottom Line
Security plugins are tools, not solutions. They protect the application layer, which is valuable, but it's the weakest layer in the security model.
Server-level protection operates below WordPress. It catches threats that plugins miss and continues to work even when WordPress is compromised. This should be your foundation.
Edge-level protection stops threats before they reach your server. This reduces load and catches attacks early. It's an easy addition that dramatically improves your security posture.
The right approach isn't choosing the best plugin. It's a layered approach where server-level protection is the foundation, edge protection adds another checkpoint, and plugins provide optional additional defense.
If your current security strategy is "I have Wordfence," you have gaps. The question isn't which plugin to add. The question is whether your hosting provider provides the foundational security that makes plugins optional rather than essential.
For more on why plugins alone create a false sense of security, see our guide on WordPress security plugins.
